Debian announced that they had a major crypto bug yesterday. Two years ago a patch was introduced into the Debian Linux distribution that was intended to eliminate a class of bug (use on un-initialised memory in a buffer) that was highlighted by a security analysis tool ( Valgrind ). In general you don't want to do this and such memory should rightly be regarded as "tainted" as it could be used as a launch pad for a bunch of injection style attacks but for a random number generator seeding function such un-initialised memory is (potentially) a useful (or at least not harmful) source of entropy. While removing this item from the code a similar line of code in another function was also removed that severely reduced the amount of entropy provided to the random number seeding algorithm and this restricted the range of random values used to generate OpenSSL keys. I haven't been able to get a definitive analysis yet but it appears that affected systems are limited to producing only 262148 pairs of distinct keys. If that is the case then this is a really serious bug. I'm intrigued by the fact that this came out just after a significant spike in SSH brute force attacks was detected by DShield (amongst others) over the past week. I'd be very interested to see if these SSH attacks were attempting to use any of the list of known suspect keys prior to the public announcement, although now that this is out in the open they are almost certainly doing that.
Most of the discussion has revolved around OpenSSH which is fair enough as that is what the vast majority of these keys will be used for but OpenSSL X.509 certs issued by any Debian based system are almost certainly also affected and if so there may be some very important cases where dodgy Debian keys are in use by people who have no idea that they were issued by a dodgy Debian distro. It's very, very unlikely that this affects any of the mainstream Certificate providers but any cases where people are using certificates issued directly by a service provider are potentially at risk.
Larry Osterman provides (as usual) a succinct and very fair explanation of the issue on his blog here.
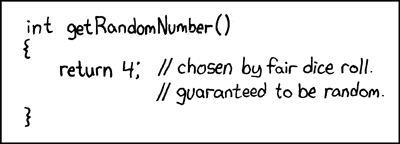
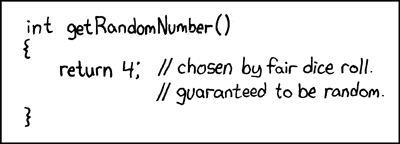
Updated to add the obligatory XKCD cartoon:
* Updated again to point out that I've just noticed that the Debian announcement uses the phrase "predictable random number generator", PRNG always breaks down to "pseudo random number generator" in my head but "predictable" is a much better way of putting it when you think about it. :)